Top Secret to RACF Migration: Complete Guide for Mainframe Modernization (2026)
Introduction
Migrating from CA Top Secret to RACF is one of the most critical steps in mainframe security modernization. However, many enterprises struggle with complexity, downtime risks, and data integrity challenges. This guide explains how RACF migration can be simplified using automation tools like VRX zMigTSS.
ENTERPRISE BLOG — MAINFRAME MODERNIZATION
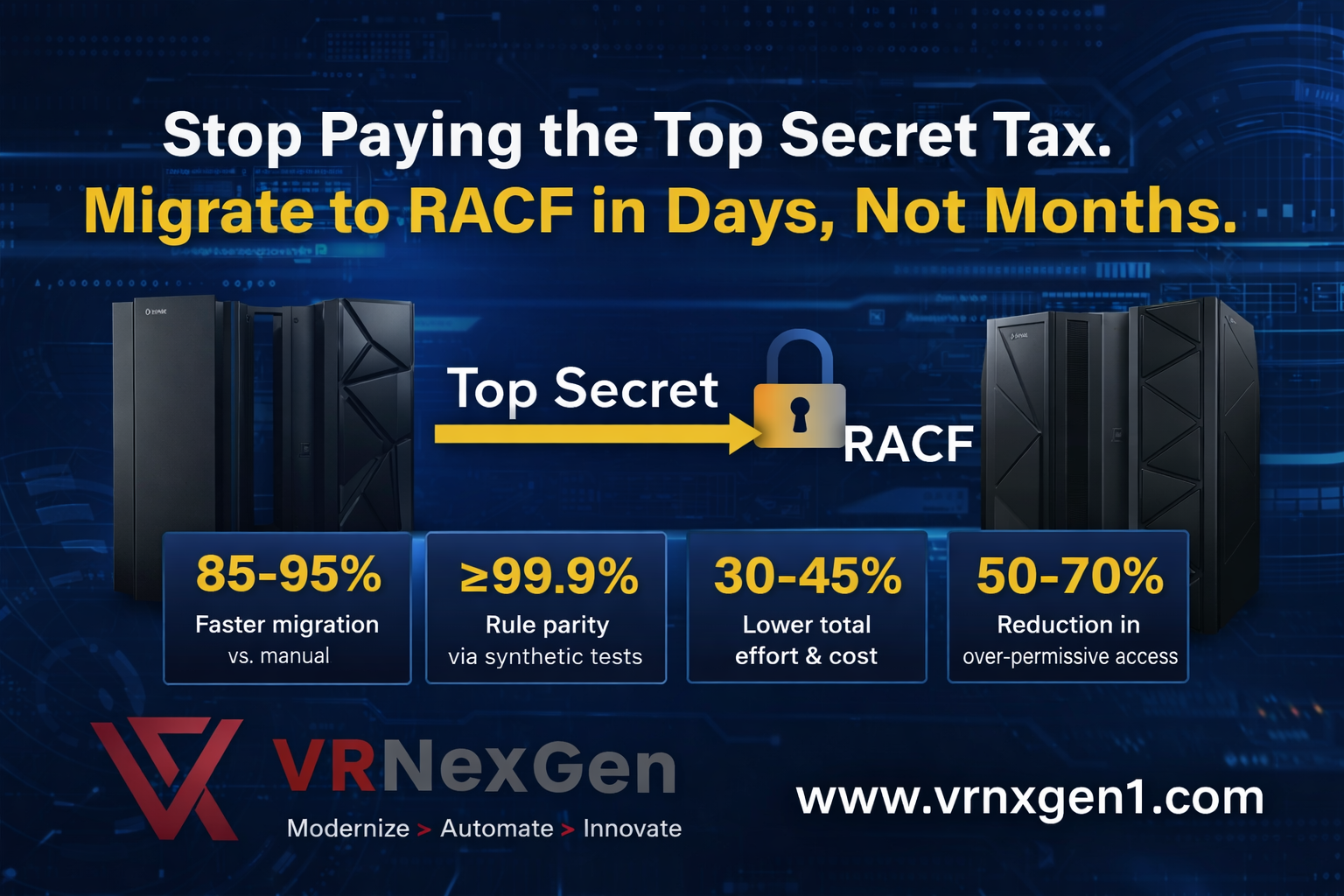
Stop Paying the Top Secret Tax.
Migrate to RACF in Days, Not Months.
Author: Vijayalakshmie | Mainframe Modernization SME & Solution Architect
Target Audience: Banking | Financial Services | Healthcare | Insurance
Solution Video: Top Secret to RACF Solution – Watch on YouTube
If your enterprise still runs CA Top Secret as its mainframe security manager, you are paying a premium licensing bill every year for a product you could leave behind — if migration were not so painful. Until now.
PROVEN OUTCOMES — VRX ZMIGTSS
85–95% Faster migration vs. manual | ≥99.9% Rule parity via synthetic tests | 0 Critical auth failures at cutover | 30–45% Lower total effort & cost | 50–70% Reduction in over-permissive access | Hours To audit-ready evidence (not weeks) |
THE PROBLEM EVERY CTO AND CISO KNOWS
For decades, the conventional wisdom in mainframe shops has been: don’t touch security. The risk of breaking a job, violating a compliance rule, or triggering a batch failure made manual migration from CA Top Secret to IBM RACF feel like defusing a bomb. So the licensing invoices kept coming.
But the landscape has changed. Regulators are intensifying scrutiny of access controls. Cloud and hybrid modernization roadmaps demand cleaner, auditable identity postures. And budget pressure on legacy software licenses — particularly third-party security managers — has reached a tipping point for Banking, Financial Services, and Healthcare organizations running IBM Z.
20,000 permit rules. Manually migrated, that is 4–6 weeks of dual-skilled SME time, with meaningful risk of over-permissive access or missed rules. Automated, it is 3–5 days — with a diff report proving parity.
WHY MIGRATION HAS ALWAYS BEEN HARD
Six Challenges That Have Stopped Every Previous Attempt
CHALLENGE | DESCRIPTION |
Semantic mismatch | TSS constructs — ACIDs, FACILITY auths, ownership — do not translate 1:1 into RACF classes, profiles, and grouping hierarchies. |
Scattered definitions | ACIDs, profiles, resources, and ownership live across dozens of TSS departments, divisions, and regions. |
Manual error risk | Hand-crafted permits miss rules, create over-permissive access, and break batch jobs at the worst possible moment. |
Audit & compliance pressure | Regulators need evidence that RACF entitlements match TSS intent and that Separation of Duties constraints are preserved. |
Zero downtime requirement | CICS, IMS, and DB2 processing cannot stop. Batch windows are tight. Any cutover must be instant and reversible. |
Scarce dual-skilled talent | Engineers fluent in both TSS and RACF are rare and expensive. Projects stall waiting for the right people. |
THE VRX ZMIGTSS APPROACH
Automation That Eliminates Every One of Those Risks
VRX zMigTSS is a production-hardened REXX automation suite built specifically for this problem. It does not simply move data — it preserves intent, enforces policy, and generates auditable evidence at every step.
# | PHASE | WHAT HAPPENS |
01 | Discovery & Extraction | REXX collectors extract every ACID, DEPT/ZONE, resource rule (DATASET, FACILITY, APPL, DB2, CICS, TCP), ownership chain, and expiry from TSS. Output is normalized to CSV/JSON with unique keys and full provenance — command plus timestamp. |
02 | Normalization & Semantic Mapping | A rule engine bridges the semantic gap: ACID → USER/GROUP, DEPT/ZONE → RACF GROUP hierarchy, TSS PERMIT → RACF PERMIT with ACCESS level translation, FACILITY/RESOURCE → RACF CLASS. FORCE and INHIBIT flags are handled. SoD policies enforced — no GROUP-SPECIAL for application IDs. |
03 | Audited Command Generation | The suite generates RACF commands — ADDUSER, ALTUSER, CONNECT, RDEFINE, RALTER, PERMIT, SETROPTS — batched by class with dependency ordering. Dry-run previews with diffs run before any production load. WARNING mode allows learn-without-fail validation. |
04 | Parity Validation & Reporting | Synthetic access tests confirm each ACID’s permissions on mapped RACF profiles. Parity diff reports highlight missing profiles, unexpected UACC, excessive permits, and orphan users. Audit pack — signed CSVs, command logs, parity evidence, approvals — is ready in hours, not weeks. |
05 | Cutover & Rollback | Short cutover window with a defined rollback path. RACF database is backed up and verified before load. Staged class activation per your timeline. Continuous batch and online (CICS/IMS/DB2) processing maintained throughout. |
The solution is built on the IBM Z platform you already own. No new infrastructure. No third-party SaaS. No dependency on consultants who have never touched a JCL deck. It runs where your data lives.
FOR THE ENTERPRISE DECISION-MAKER
What This Means for Your Organization
BENEFIT | WHAT IT MEANS FOR YOUR ORGANIZATION |
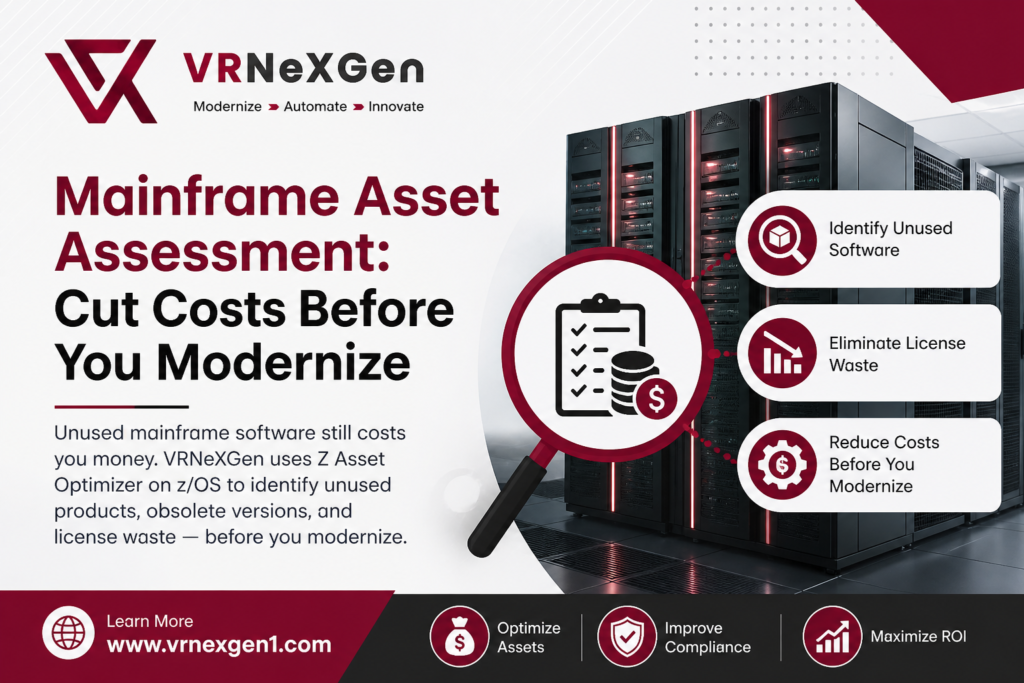
License Cost Elimination | Remove the CA Top Secret annual license from your budget entirely. IBM RACF is already included with IBM Z — you are already paying for it. |
Regulatory Confidence | Audit-ready parity evidence — signed CSVs, command logs, access test results — delivered hours after cutover, not weeks later. |
Tighter Security Posture | 50–70% reduction in over-permissive access as UACC is tightened and SoD policies are enforced during migration — not as a separate cleanup project. |
No Dual-Skill Dependency | Automation does the heavy lifting. You do not need to find and retain the rare engineer who knows both TSS and RACF deeply. |
Business Continuity | Continuous batch and online processing throughout the migration. Your CICS regions and IMS transactions do not pause for a security project. |
Predictable Timeline | From discovery through cutover in days — not a multi-quarter programme. Budget certainty. Board-level commitments kept. |
SECTOR CONTEXT
Why Banking, Healthcare, and Financial Services Move First
For regulated enterprises, the calculus is especially clear. Banking and capital markets firms face PCI-DSS, SOX, and DORA obligations that demand demonstrable access control evidence. Healthcare organizations under HIPAA need audit trails proving minimum necessary access. Insurance carriers and asset managers carry their own regulatory reporting burden.
In each case, the migration is not just a cost-reduction exercise — it is a compliance posture improvement. Moving to RACF with tightened UACC and enforced SoD policies leaves the organization in a measurably stronger security position than it was with Top Secret, not merely an equivalent one.
And unlike a theoretical future migration, VRX zMigTSS is a repeatable, tested process. The same automation that ran on one client’s 20,000 permits runs on yours. The rule engine, the parity tests, the audit pack format — all are hardened through production deployments.
Why Enterprises Are Moving to RACF
Include:
- Cost reduction
- Security standardization
- IBM ecosystem alignment
SOLUTION WALKTHROUGH
See VRX zMigTSS in Action
Watch the full technical walkthrough — Top Secret to RACF migration, automated end to end:
Video Link: Top Secret to RACF Solution — VRX zMigTSS (YouTube)
Ready to eliminate your Top Secret license?
Talk to Vijayalakshmie and the VRNeXGen team about your environment. We will scope the extraction, map your ACID inventory, and show you what the timeline looks like for your organization — in a complimentary discovery session.
About the Author
Vijayalakshmie is a Mainframe Modernization SME and Solution Architect at VRNeXGen Technologies, specializing in automated mainframe security migration, RACF implementation, and compliance engineering for regulated enterprises in Banking, Financial Services, and Healthcare.
Need help with RACF migration?
Contact VRNexGen experts for secure, automated migration solutions.
🌐 https://vrnexgen1.com/contact/
Read our detailed RACF migration guide here:
👉 (Medium link)
Frequently Asked Questions
- What is RACF migration?
- How long does RACF migration take?
- What are risks in Top Secret migration?
- Why use automation tools like zMigTSS?